
Last spring, a dentist received a $4,200 invoice for phone services. During two evenings, an overseas caller used the clinic's system to reach high-cost lines after hours. Although the service provider returned some charges, full recovery never happened. Ten minutes resolved the issue - after discovery. For twenty-four months prior, no one reviewed those records at all. Oversight allowed loss.
Here begins a tale often told, yet rarely fresh. Prior to examining VoIP security tips for business in practice, observe this plain fact: corporate VoIP security for business tends to be basic upkeep - affordable, nearly every time. Damage strikes those firms having viewed telephony much like an appliance, switched on long ago, then left untouched ever since.
Is VoIP secure? The honest answer
True, in most cases. Yet absence of automatic activation remains.
Despite appearances, digital conversations travel under lock using TLS and SRTP when configured correctly - that is genuine VoIP encryption. Physical wire taps face little resistance - thirty dollars buys enough gear to intercept analog transmissions freely. Where old lines offer silence by default, they grant openness to eavesdroppers instead. Security tilts toward internet-based voice systems when privacy stands in question.
Here lies the issue: setup matters. Left untouched from origin settings, a VoIP system exposes port 5060 publicly while using default login credentials - essentially an invitation. Automated tools actively search for such openings without pause. Place a new PBX online via a cloud host now, detection follows swiftly. Minutes may be all it takes.
The answer to "is VoIP secure" relies solely on activation of built-in safeguards. Whether those protections function hinges on user setup choices made during deployment. Proper configuration determines risk level more than design flaws do. Default settings often remain weak unless changed deliberately. Protection exists but only activates when enabled by operator action.
VoIP vs landline security - what actually changes
Two things flip when you move to VoIP.
Consider how much wider exposure becomes. Unlike a landline tied to isolated wiring, VoIP shares infrastructure with computers, cameras, printers - devices already online. Breach any single point, access spreads silently across shared links. Phones become reachable once defenses weaken elsewhere. This happens more than assumed - the real downside of VoIP vs landline security.
Landlines lack features now possible through modern systems. Security measures like encrypted channels appear alongside tools such as multi-step verification. Permissions for specific calling activities can differ by user. Suspicious numbers may be blocked automatically, without intervention. Monitoring occurs continuously during active sessions. Traditional phone networks do not support these capabilities. Increased access points bring higher risk - yet also open paths to stronger protection. Are VoIP phones secure? Should you choose this path, advantage follows - provided safeguards are applied. A different expense pattern emerges after transition, as previously detailed in the VoIP vs traditional phone comparison.
The VoIP security risks that actually hurt businesses
Among the many lists circulating, twenty-five threat types appear frequently. These often rest on speculation. What follows reflects only what appears in actual incident documentation - the VoIP security risks and VoIP security threats small and mid-size firms actually face. A shift occurs when theory meets observation.
1. Toll fraud (VoIP fraud). One type stands out above others. Overnight calls stack up when attackers take control of a phone line. Premium destinations receive repeated dialing, unseen until invoices arrive. Billions vanish annually - figures suggest near $40 billion across nations. Smaller firms face greater risk; their oversight lacks depth found in larger organizations.
2. Vishing and VoIP phishing. Vishing, also known as voice phishing, tricks people through phone calls. Instead of showing the real number, caller ID appears to come from trusted sources - banks, company leaders, even tax authorities. Workers may disclose sensitive details: access credentials, multi-factor authentication codes, funds transferred without verification. Performance of these VoIP phishing scams improved sharply since 2024 due to synthetic voices mimicking real ones. Deception now sounds convincingly human.
3. Eavesdropping on unencrypted calls. Listening happens when calls lack encryption. When data moves across the open internet without TLS or SRTP, interception becomes possible. Anyone positioned along the path may capture sound. Public networks in cafes present clear dangers for employees on trips. Audio travels exposed under these conditions.
4. SIP scanning and credential stuffing. It begins with automated tools probing SIP interfaces, searching for openings. Following that, repeated attempts occur using widely known login details. Access gained leads directly to unauthorized call usage. The most frequent entry point? Insufficient protection on SIP account credentials. This remains the dominant VoIP vulnerability within live systems and the main reason SIP security deserves its own checklist.
5. Denial of service against your PBX. Service disruption targeting your phone system occurs infrequently, yet remains a genuine risk. A surge of meaningless data overwhelms the SIP infrastructure, disabling voice communication. This chaos sometimes hides theft attempts or demands for payment. Silence on the line may signal hidden activity beneath.
6. Insider misuse. One former worker kept logging in after leaving the company. Despite policies, their access remained active for months. Each week, a salesman shares data with a relative overseas during routine phone calls. Access that should have been restricted was never reviewed. A temporary hire holds elevated permissions without proper oversight. These VoIP security issues repeat often across industries. Common? Yes. Harmless? Far from it. Financial impact adds up silently over time.
12 VoIP security best practices that move the needle
What stops problems most often guides this list of VoIP security best practices, not what reads well in marketing material. Far greater impact comes from the initial half compared to the later entries. Reaching into your pocket for two hundred dollars versus fourteen thousand hinges on those top three items alone. If learning how to secure VoIP from one list, this is the one.
- Cap international dialing by default. Usually, smaller companies do not contact places like Sierra Leone, Cuba, or high-cost satellite networks. Instead of allowing everything, restrict access through the provider or phone system, then allow only necessary destinations. One adjustment like this stops most long-distance VoIP fraud almost immediately.
- Use long, unique passwords on every extension. Each add-on requires distinct, lengthy access codes. Avoid sequences like 1234. Steer clear of digits matching the extension ID. Company labels are poor choices too. Relying on tools that create twenty-character unpredictable sets proves useful. Brief credentials fall quickly under automated attempts. Given time, robotic probes dismantle simple entries.
- Turn on VoIP encryption: TLS for SIP, SRTP for media. Encryption must be enabled. Though widely supported today, these features often remain disabled upon setup. Look into the configuration options tied to your service account. When secure SIP is missing from what is provided, another service should replace it.
- Set a daily and monthly spend cap. Should expenses rise unexpectedly, limits prevent severe outcomes. When typical charges reach two hundred dollars each month, allow up to four hundred. Fraudulent long-distance calls often generate thousands overnight. With controls in place, damage stays manageable rather than devastating. Limits turn extreme risks into mere inconveniences.
- Enable multi-factor authentication on the admin portal. Access to the admin portal must include MFA. The PBX administrator account functions as a primary control point. Should that credential be compromised, total system access may follow. At minimum, implement MFA using an authenticator application - avoid SMS-based verification entirely.
- Restrict SIP to known IP addresses where you can. Should devices operate within a single office location, permit SIP communications solely through that site's assigned IP segment. Remote employees find better protection via secure tunneling methods or dedicated applications supplied by service providers. Exposure of SIP interfaces to open networks ceases under such arrangements - the cornerstone of practical SIP security.
- Disable extensions you do not use. Former staff members still appear on systems sometimes. That front desk station removed last year remains active behind the scenes. Each inactive line could open the network to intrusion. Check access points every three months without exception.
- Train staff on vishing and VoIP phishing. Because trust opens doors, voices deceive. Staff learn through frequent brief exercises, never just annual videos. A single habit blocks most attacks: if a caller demands urgency, disconnect immediately. From memory, each person knows what follows - contact must come only through verified numbers already held internally. Repetition makes response automatic.
- Keep firmware patched. Security patches require regular attention. Desk phones need updates just like PBX systems. Session border controllers also fall into this category. Updates exist - but rarely install themselves. A manual check remains necessary. Mark dates ahead of time. Reminders help maintain consistency.
- Look at the call log every morning. Every morning begins with reviewing the call record. Not impressive at first sight. Yet it reveals all irregularities early. A brief check - just 120 seconds - over recent outgoing calls detects unauthorized toll usage immediately, not weeks later. Should someone fail to notice, losses grow fast. Many service operators supply a daily report by electronic message, provided the request is made.
- Segment voice traffic on your network. Isolate voice communications within the network structure. A dedicated VLAN handles VoIP separately. When ransomware infects an office Wi-Fi device like a laptop, access to the PBX remains blocked. Improved audio performance emerges - less interference occurs during peak data usage hours. One reason? Streaming activity no longer shares the same path.
- Pick a provider that takes security seriously. A choice of provider matters where security stands firm. Should questions on encryption go unanswered, consideration shifts elsewhere. When inquiry meets indifference - especially around SIP scanning - the path leads away. Responsibility divides, yet the service supplier handles critical layers of VoIP cyber security. Cost at the lowest point often means strength in safety falls behind.
What you actually get from a serious provider vs DIY PBX
A cloud-based Asterisk setup works well only when maintenance tasks are handled regularly. Should updates fall behind, risks emerge quietly over time. Without dedicated oversight, system flaws may go unnoticed until problems arise unexpectedly. Many smaller companies lack such support roles internally. Consequences often surface after an incident occurs.
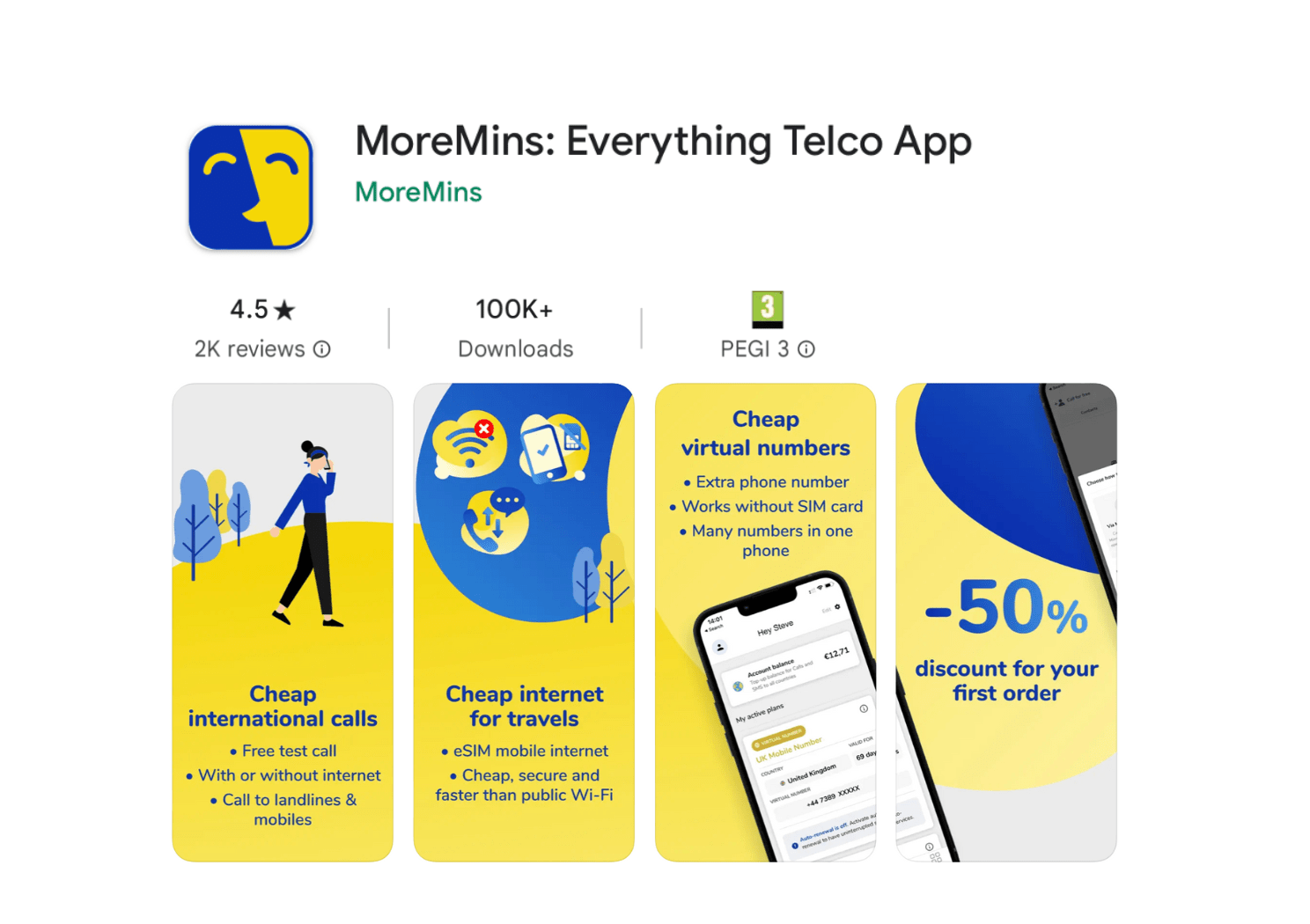
A managed VoIP solution such as MoreMins virtual numbers includes built-in protections, active right away. By default, both signaling and audio remain encrypted. Instead of exposure, SIP connects through filtering systems that block scan attempts ahead of arrival. Behavior showing risk raises immediate internal alerts. Updates requiring manual firmware fixes do not apply here.
| Security control | DIY self-hosted PBX | Managed VoIP (MoreMins) |
|---|---|---|
| TLS + SRTP encryption | Manual, often misconfigured | On by default |
| SIP scan filtering | You build it | Built in at network edge |
| Toll fraud monitoring | You write the alerts | Automatic anomaly detection |
| Firmware patching | Your problem | Handled by provider |
| MFA on admin portal | Depends on stack | Standard |
| Spend caps and daily summaries | You configure | Available out of the box |
Vishing and VoIP phishing - the human layer
Stopping machines often relies on the safeguards outlined earlier. Yet vishing operates differently - people target people directly through such methods. A ringing phone interrupts routine. An apparently credible individual offers an explanation that seems logical. Funds move without delay when authority appears to demand it. Eighty thousand dollars transfers after someone claims the chief executive cannot be disturbed.
By 2024, voice replication had deepened the risk of VoIP phishing. A mere three seconds from a professional video could reproduce speech accurately. Recognition of sound alone offers little protection now. Fake caller data spreads without effort. Therefore, reliance on auditory identity fails. Dependence on displayed digits also fails. What remains must rest on structured steps.
The rules that truly function tend to be brief:
- A call asking for payment details, a password change, or an authentication code is followed by a return call. The number used comes from the company's official internal list - never from what the speaker on the line provides.
- Approval by two individuals required for any transfer exceeding a limit appropriate to the organization. One person alone cannot authorize such transactions. The threshold depends on operational needs.
- A quiet signal during mimicry of leadership. Seems odd. Functions. Yet remains simple. Stands firm without flair.
- Reporting fraud should feel simple. When the process feels like effort, silence follows instead of statements. A smooth path for saying "this felt wrong" invites more voices. Friction keeps people away from speaking up.
Most attempts cannot be blocked. Still, those leading to real losses often are stopped. Though not perfect, protection works where it matters most.
SIP security in two paragraphs
Should only one point stick from this guide on business VoIP security - secure SIP thoroughly. This protocol handles call initiation. Normally it operates over UDP or TCP at port 5060. That entry draws constant scans online, second only to SSH traffic. Any corporate phone system revealing unprotected SIP to external networks faces inevitable attacks.
A SIP security solution builds across levels. Communication shifts to SIP via TLS rather than unsecured UDP channels. A session border controller stands before the PBX - alternatively, service comes from providers including such protection. Requests from nations outside operational regions face blocking by rule. Too many login tries trigger enforced delays. Lengthy, unpredictable SIP passwords matter more than easy-to-remember phrases. Avoiding even one standard step opens paths to toll fraud, though none seem extraordinary at first glance.
Where to start this week
Should time be limited, focus on these VoIP security tips for business above others. Begin with clear priorities instead of rushing forward blindly. Following that, adjust steps based on what unfolds. Finally, observe outcomes before deciding next moves.
Early today, look through your phone system's outgoing calls list. Should there be unfamiliar entries - particularly those overseas or high-cost - contact your service operator without delay. Unidentified activity means act now, rather than wait. Numbers from unknown regions require immediate attention. Midnight connections may carry consequences best addressed at once.
A limit on spending comes first. A barrier against overseas access follows. Ten minutes handles both tasks. Worst losses stay within reach of your budget.
Where passwords are brief or reused across accounts, substitution becomes necessary. When carried out completely, this step blocks the majority of fraudulent charges typically encountered.
Other items on the list matter just as much. Yet it is these three that separate modest charges from overwhelming ones. Shifting small firms away from outdated office systems to virtual phone numbers has shown a clear pattern. Each case begins when one of these issues appears without warning.
Should simplicity matter in your communication tools, consider the way MoreMins manages low-cost global calling for companies. Alternatively, obtain a UK-based virtual phone number or a United States virtual number within moments. Each option reduces effort through pre-built VoIP security best practices.
Most security incidents stem from simple oversights. A preset password often opens the door. An exposed SIP interface invites trouble. Voice deception targeting financial staff succeeds too easily. Address these points first - improvement follows naturally. Other items demand attention, though less urgently. Global dialing limits matter. So does daily spending control. Ten focused minutes clarify both.
VoIP security for business - frequently asked questions
True, if configured properly. Modern VoIP systems use TLS for signaling, SRTP for voice - both exceed the security of old copper landlines. Yet flaws often arise not from weak tech but missteps: unchanged default credentials, exposed SIP interfaces, missing multi-factor authentication on management portals. Fix these points, however small they seem, and the resulting setup surpasses legacy phone lines in safety.
First comes toll fraud - when unauthorized users run up charges through expensive call routes. Following that, vishing emerges, blending fake caller identities with psychological manipulation. Next, automated login attempts exploit weak extension passcodes. Conversations without encryption risk exposure to silent monitoring. Interruptions in service may stem from targeted floods overwhelming system capacity. Lastly, threats come from within, when authorized individuals exceed permitted actions. Highest financial impact overnight typically ties back to fraudulent calling activity.
Confidentiality varies by setup. Where physical access exists, traditional phone lines offer no protection - sound travels openly across wires. When secured using protocols like TLS plus SRTP, digital voice transmissions become encoded from start to finish. Viewed strictly through that lens, internet-based calling outperforms when correctly arranged. A single network carries both VoIP and other data, meaning an intrusion might extend to calling systems. When protections are active, voice over internet tends to resist threats better than traditional phone lines.
Begin by addressing low-cost yet effective steps. International calling should be restricted first. Strong, distinct passwords are required for each extension. Multi-factor authentication must apply within the admin interface. Transport Layer Security along with Secure Real-time Transport Protocol needs activation. Limit SIP access only to recognized IP addresses whenever possible. Daily inspection of call records helps detect anomalies early. Firmware updates for the PBX cannot wait. Staff require instruction on voice phishing attempts. A defined procedure applies when someone requests payments or credentials via telephone. Many fixes fit into a single workday. These actions stop common attack methods effectively.
Someone takes control of your phone setup without permission. These unauthorized users often connect to high-cost overseas lines during nighttime hours. The charges appear on your account afterward. Annual damage across businesses reaches approximately 40 billion dollars. Security begins with simple steps instead of complex tools. Blocking unnecessary foreign routes reduces exposure significantly. Daily spending limits stop runaway costs before they escalate. Inactive access points should remain turned off at all times. Strong credentials for SIP accounts slow down intrusions effectively. Reviewing recent activity each day helps catch issues early. Providers that monitor traffic patterns automatically offer stronger protection overall.
True, there exists no visible effect whatsoever. Though TLS plus SRTP introduce minimal overhead - measured in low millisecond figures - the impact remains imperceptible. Given today's standard connections, delays dissolve into background noise. Audio clarity shows identical behavior whether encryption runs or does not run. Absent any strong justification, disabling protection makes little sense.
The protocol responsible for initiating a VoIP connection is called SIP. Typically operating on port 5060 via UDP or TCP, it draws frequent scans across global networks. To enhance protection, encryption through TLS replaces unsecured UDP transmissions. Positioning a session border controller before the PBX adds another layer. Limitations applied to registration tries reduce unauthorized access risks. Strong, unpredictable credentials further deter intrusion attempts. Omitting even a single safeguard increases vulnerability to fraudulent usage significantly.
Indeed. Some nations provide a complimentary digital telephone line for testing purposes. Alternatively, verification texts arrive through an internet-based number before moving forward with subscription options suited to operational needs. Commitment-free arrangements apply, beginning at 0.99 dollars each month.

